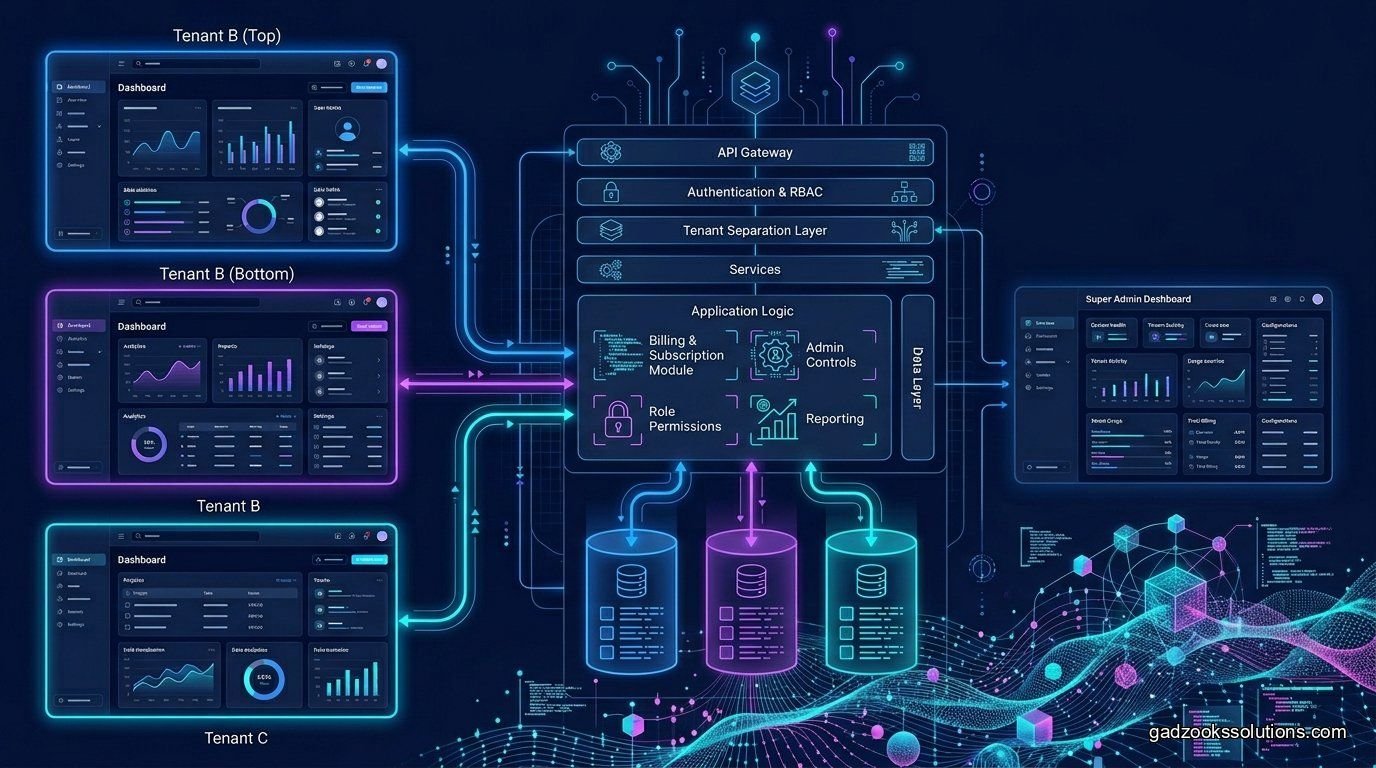
The hardest part of building a SaaS isn't the features—it's the multi-tenancy. You need to ensure that Company A can never, under any circumstances, see Company B's data. Achieving a robust **multi-tenant SaaS architecture Node.js** setup requires a deep understanding of data isolation, subdomains, and database schema design.
Three Ways to Isolate Data
When designing your **multi-tenant SaaS architecture Node.js** backend, you have three primary choices for data isolation:
- Database-per-tenant: Total isolation, but a nightmare to manage at scale.
- Schema-per-tenant: A middle ground using PostgreSQL schemas. Good for security, harder for migrations.
- Shared Database (Row-Level Security): The modern standard. All data is in one table, but a `tenant_id` column and Postgres RLS ensure users only see their own rows.
PostgreSQL Row-Level Security (RLS)
This is our favorite approach for **multi-tenant SaaS architecture Node.js** projects. By enabling RLS in PostgreSQL, you can define policies that automatically filter every query based on the current user's session. This means even if you forget a `WHERE tenant_id = ?` in your code, the database will catch it and prevent data leakage.
Technical Insight
We use a Middleware in Express/Fastify that extracts the tenant information from the JWT or Subdomain and sets a local 'current_tenant' variable in the Postgres transaction. This ensures the RLS policy knows who is asking for data.
Managing Subdomains and Custom Domains
A true **multi-tenant SaaS architecture Node.js** needs to handle `client1.yourapp.com` and eventually `dashboard.client1.com`. We recommend using a reverse proxy like Caddy or Nginx with an automated SSL provider (like Let's Encrypt) to handle these dynamic domain requests without manual configuration.
The Gadzooks recommendation
Don't gamble with your users' data. Gadzooks Solutions builds production-ready **multi-tenant SaaS architecture Node.js** systems that are secure by default. We help you choose the right isolation level and build the infrastructure to support millions of tenants.
Frequently Asked Questions
Is Row-Level Security (RLS) slow?
When indexed correctly, the performance hit is negligible. For 99% of SaaS applications, the security benefits far outweigh the millisecond-level difference in query time.
How do I handle migrations across thousands of schemas?
This is why we prefer the shared database approach. Migrating one table is infinitely easier than running the same migration script 5,000 times across 5,000 schemas.
Can I give each tenant their own encryption key?
Yes. This is called 'Envelope Encryption.' You store a Master Key for each tenant and use it to encrypt/decrypt their specific data rows. This provides an extra layer of security beyond RLS.